I’m going to start sharing little techie tidbits that require me to go scour the Internet for exactly how to do them, in hopes of making you able to do it in a lot less time than it took me!
So I’m having trouble with connection times spiking to an Amazon Web Services ELB, so it’s time to break out the tcpdump to take packet traces and the wireshark (was ethereal long ago) to analyze it. I’m on OSX El Capitan (10.11.6).
tcpdump comes on OSX (or if it doesn’t, something installed it without me knowing!). Step one is figure out what network interface you want to dump. This will list all your network interfaces.
networksetup -listallhardwareports
Then, run a packet trace on that interface. I’m using en0 the primary wireless interface, so I run:
sudo tcpdump -i en0 -s 0 -B 524288 -w ~/Desktop/DumpFile01.pcap
I go to another window and hit the URL I’m having trouble with – you can use whatever, but I used ab (Apachebench) which comes with OSX. Other popular URL-hitters you might install are curl, wget, and siege.
ab -n 10 http:///
Then come back and control-C out of the tcpdump capture. Now I have a network dump of me hitting that URL (plus whatever other shenanigans my computer was up to at the time, so there’s probably a lot of noise in there from chat clients etc.).
Now to analyze it – wireshark. I had to go a couple rounds with the installation.
If you want the UI you need to install it as:
brew install wireshark --with-qt
(If you just install wireshark without –with-qt you don’t get wireshark, you get a command line called tshark, and then you need to reinstall…) For this, as with most things, you need Xcode or at least the Xcode command line tools (I always just install the tools). You install them with:
xcode-select --install
But if you have an older version (<8.2.1) the wireshark build will fail. To update the command line tools, you… Apparently you don’t any more. The App Store doesn’t offer Command Line Tools updates and Apple has gotten more unclear and squirrelly about whether they’re even a thing. So I just installed full XCode from the App Store, whatever, it’s just network and disk space and contributing to the heat death of the universe, but I’m not bitter, and then it builds.
Optionally if you want to capture from within wireshark on your local box instead of having to tcpdump separately also do
brew cask install wireshark-chmodbpf
But to analyze your tcpdump file just run
wireshark
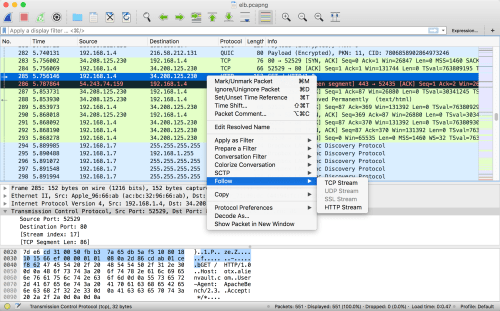
And load in the capture file. The quickest way to then sort into what you want is to find one part of a transaction of interest – like in my case by filtering on “http” or just looking around – and then right-clicking on one packed and saying “Follow… HTTP stream” and you get a whole transaction end to end.

And now you test out your TCP/IP network admin knowledge by rooting through and seeing if you can find what’s going wrong!

Hello,
Why you build wireshark via brew instead of downloading native installer? Here is link and it works well on osx. https://www.wireshark.org/download.html
With all due respect – why would I want to install something not via brew? Like why would I install something by hand instead of from yum or rpm repos? Because I love navigating people’s crufty Web sites and undocumented github repos? Nope, if it’s not in brew so I can easily install and upgrade it I think twice about whether I really need that or not. The day that people can be a “special snowflake” install have luckily mostly gone by.
to be fair, you don’t need to download and install the entirety of Xcode to get it off their website
Um… I think you do now? Like I mention in the article you can’t just get the XCode command line tools any more. If you have a way to do so please share…
the –with-qt option does not work anymore
brew cask install wireshark installs the gui after installing the command line
–with-qt is throws an invalid option error.
This is with wireshark 3.2.6
Without that option, also on el capitan, I then get a bunch of syntax errors related to nghttp2.rb
Sadly, the version of wireshark they distribute on their website requires 10.12 or later.
brew install –cask wireshark