I just got back from DevOpsDays Austin, and it’s always great to go out and talk with a wide array of folks from the tech community to see what’s up.
The takeaways were interesting. Austin is an advanced tech hub, but hasn’t been bitten by the AI bug as hard as SFO. On the one hand that worries me that our community might be getting behind, but there’s some justified bubble avoidance too.
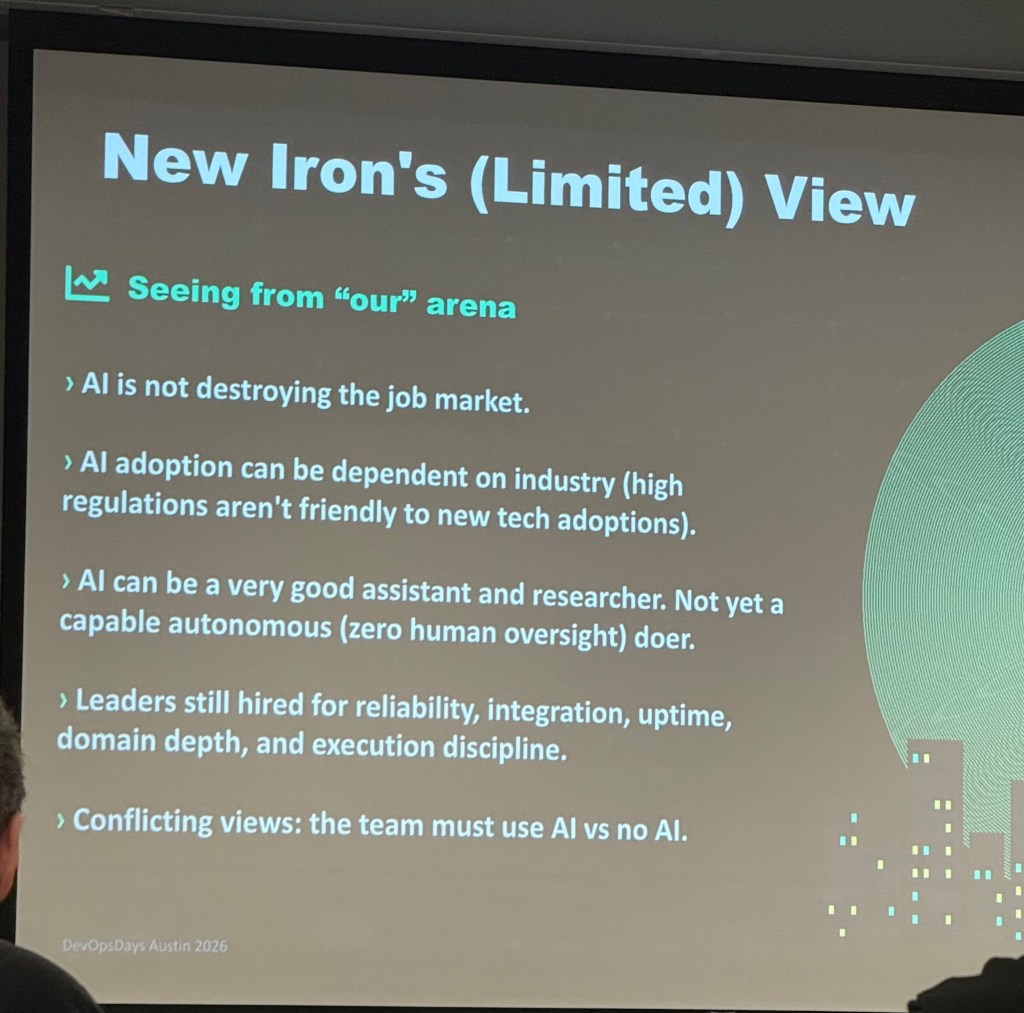
Takeaway One: AI adoption is on a curve like everything else. It is a sharp curve, but out in real businesses there’s still a sharp divide between AI’ers and non-AIers. Will Longenecker from elite tech recruiting firm New Iron shared some data from their work and it provides a much more moderate view of AI and the workforce. There’s some shops pro, some shops anti, some shops going nuts with tokenmaxxing, some shops containing costs, and so on.
Takeaway Two: Attitudes to AI are maturing. It’s been a rough road with AI in that there’s a lot of real awesome tech there, but the oligarch set has been blowing it into a bunch of ridiculous claims, so it’s a giant spike that’s 50% real value but 50% bubble. I found that the group was in general very AI forward and most people were using it in some way, but that there’s a real appreciation for the challenges and ROI evaluation and not just bandwagon hype.
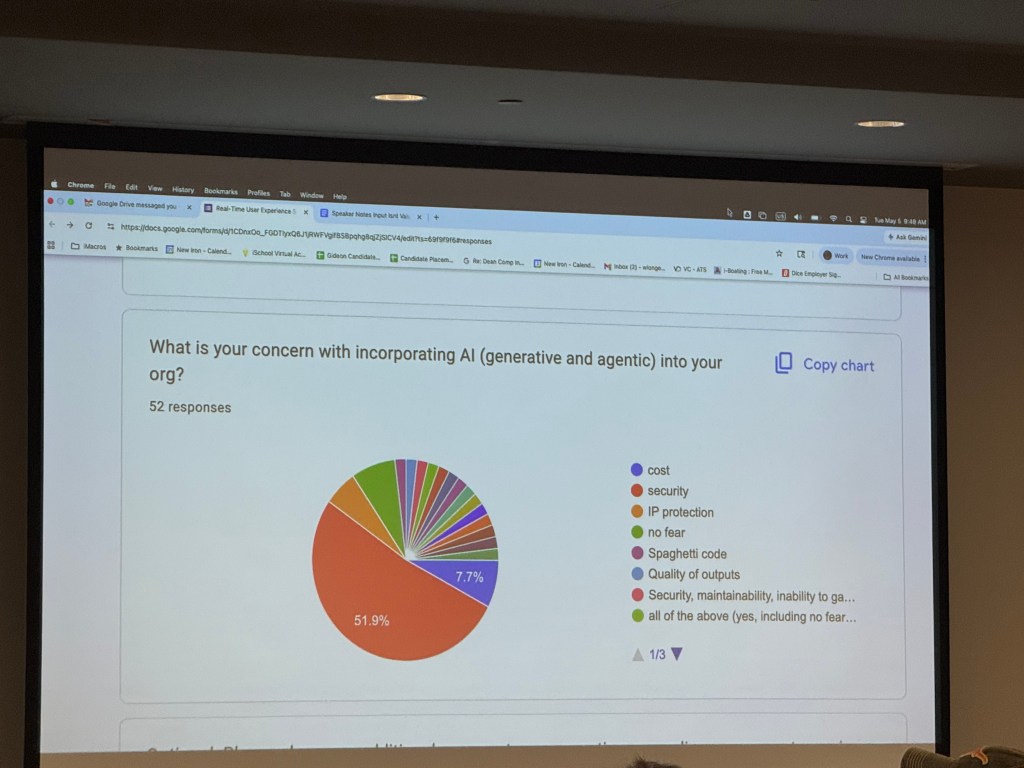
Will did a flash survey of the group, and the interesting takeaway is that over 50% of the respondents felt security was the #1 concern with using AI agents. Other speakers and groups of practitioners at the conference talked about cost, quality, and so on.
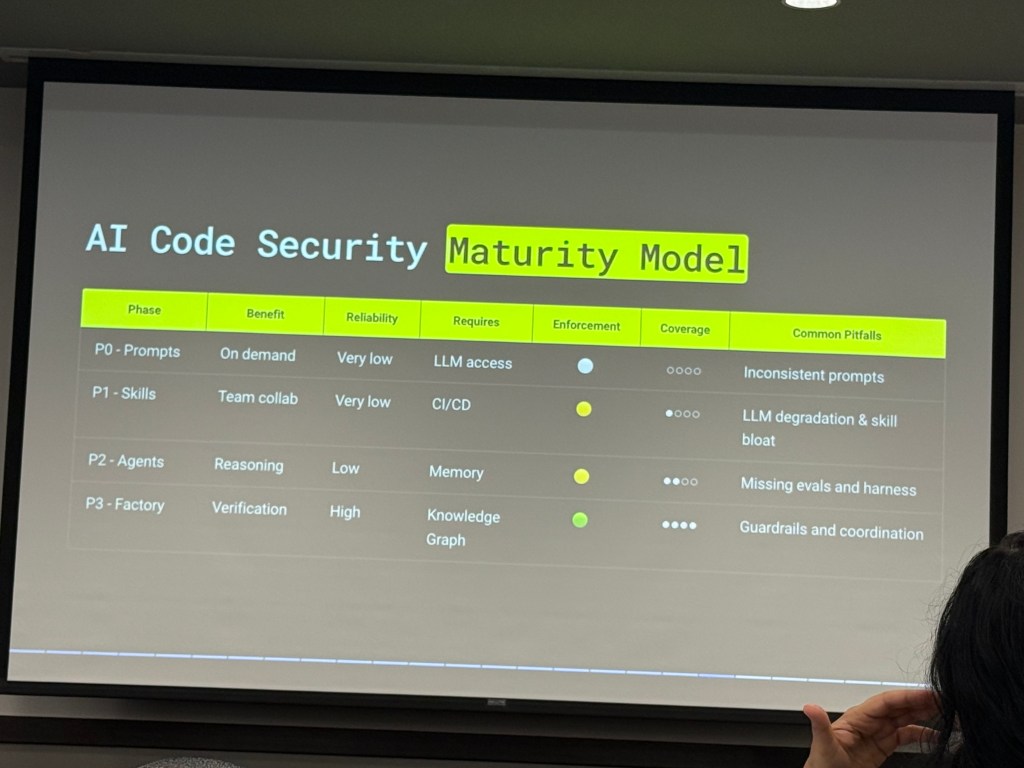
But they weren’t just talking about it in terms of “it means it’s bad,” these folks are already trying to develop practices and tooling to mitigate it.
From a DevOps perspective, the basic description of what’s been going on in the industry it that for a long time, the technology value chain had one big, long, expensive link – software development – and a bunch of smaller links like product, testing, operations, and so on. It’s been 100 devs to a handful of SREs, security pros, and so on. Which worked when it took a long time to produce software. So companies hired up truckfuls of devs, and paid them whatever they wanted, because that’s what made the value flow.
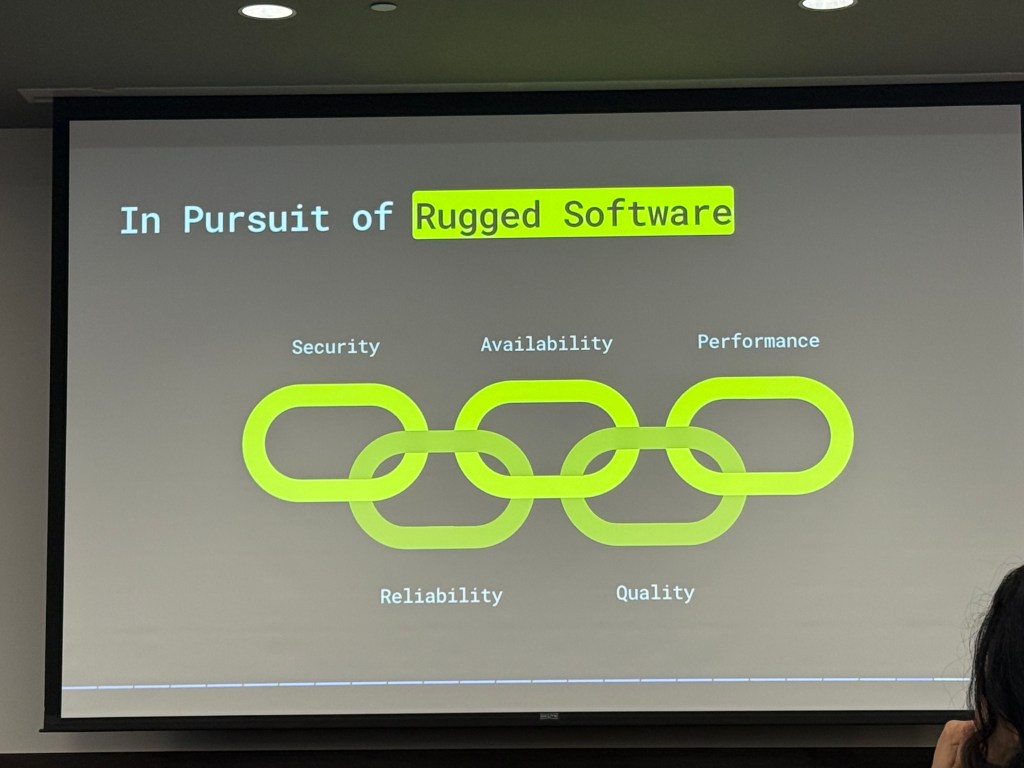
Now producing software is much faster and less expensive, and more can be done by Product and those other links in the chain. So you see developer layoffs. But even if you lay off 20% of your devs, they are all suddenly generating code at 10x the rate. The ratio in the chain of security, quality, operations, and so on was not great in the first place but now it’s completely untenable. This is forcing an evening out of that value chain, both with more tools but also the staffing and focus has to step up. AI is not generating secure, quality, performant software – the models are trained on all the crappy software out there in the wild!
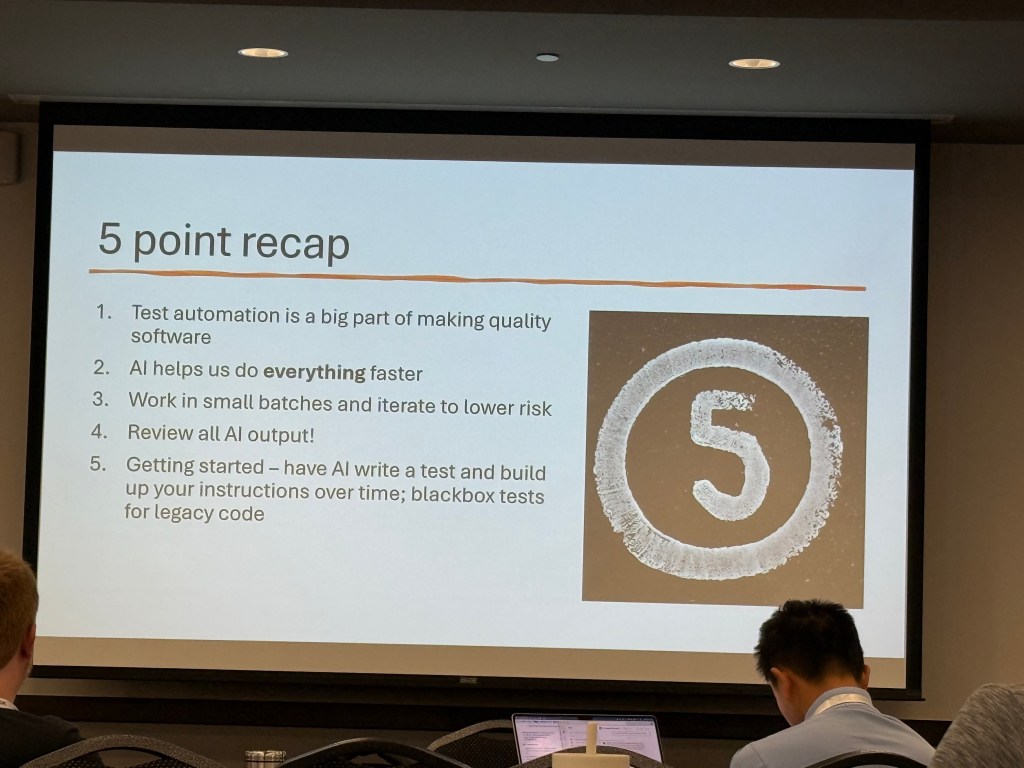
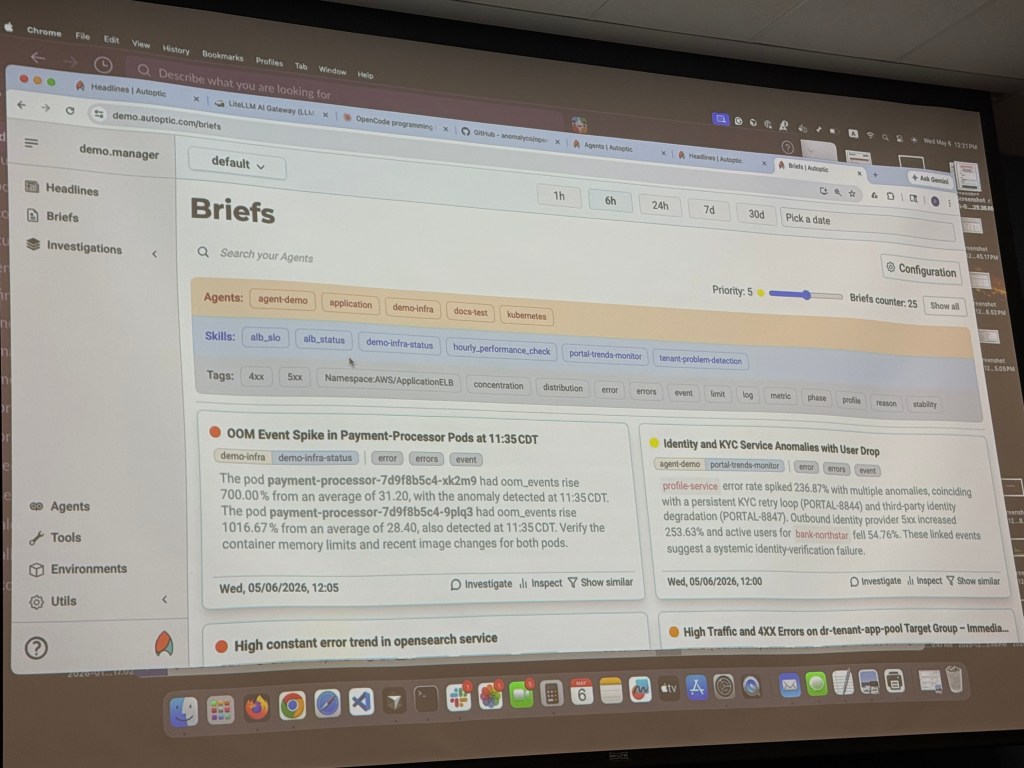
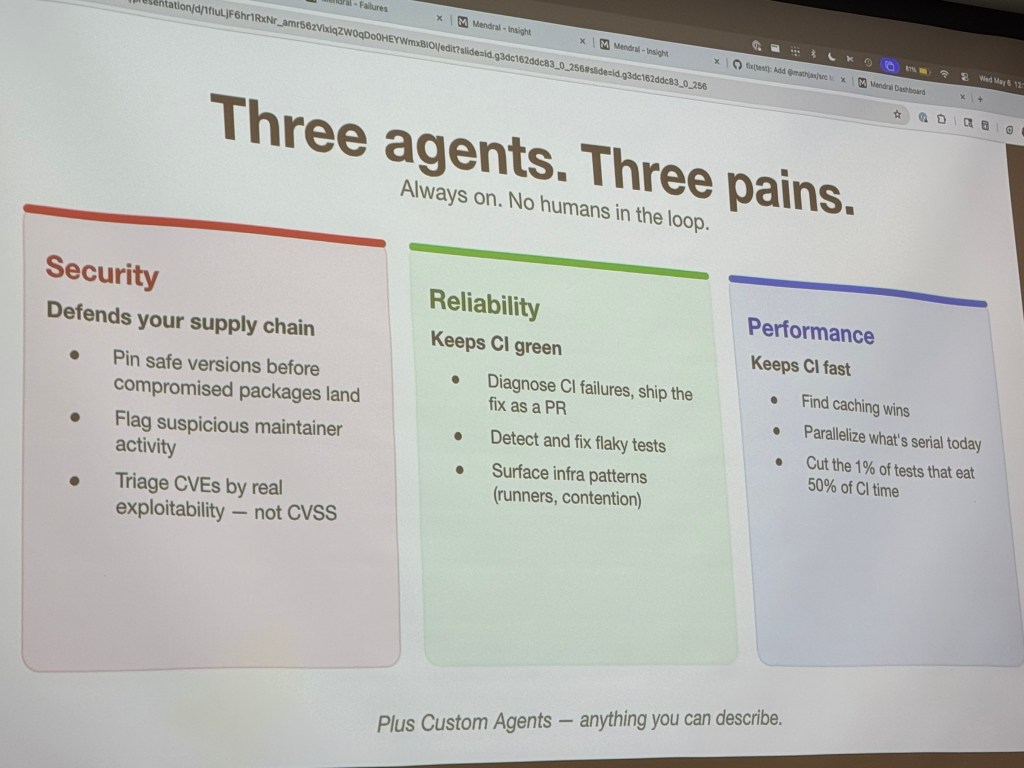
So the talks and startup tools were on how do you test more effectively,
How do you secure more effectively.
operate more effectively.
Build more effectively,
Manage your cost effectively.
And so on. Basically the good old rugged software model.
The “tokenmaxxing” and “it must be alive” hype cycle is running out and companies and tech practitioners are buckling down to the realities of “OK, so this will get me a 20% overall advantage. Great!” 10x speed is 10x slop speed and is expensive once the token subsidies end and puts your company at risk. But, smart orgs will use the resources freed up by the “faster typing” part of the benefit to find much better solutions than they’ve had so far in these areas – to be honest the hard part has always been making software enterprise ready and many orgs have suffered calamity from not doing it well. With software now pouring out of every open faucet, leveling up in these disciplines is the new path to success.
That’s not a surprise, it’s the same “Operations is the new secret sauce” message from the Web growth era, but is forcing advances in thesse other fields as well – security, ops, etc. had to adapt to keep pace in Web 2.0 but they are still slower and more manual than is needed in this new world.
I think of it like the transition from servers to virtual servers to cloud servers to containers to kubernetes – it pushed the entire industry from manual config and runbooks to configuration management to declarative infrastructure to pervasive orchestration. AI is that same forcing function – it’s not eliminating net tech jobs or anything like that, it’s just moving them around in an inevitable way. And sure, half the silly chatbots added to every product will eventually fade away as adding no value, but AI as a ubiquitous system component is here to stay.